Proton Mail has become a cornerstone for privacy-conscious individuals in 2026, offering encrypted email services that prioritize user security. In a recent guide by CyberInsider, the focus is on how Proton’s ecosystem, spanning services like ProtonVPN, Proton Drive and Proton Pass, works together to protect your data. For example, Proton Mail employs end-to-end encryption, making sure that only you and your intended recipient can access your messages, even if intercepted. This guide also highlights Proton’s compliance with Switzerland’s stringent privacy laws, which provide a legal framework that minimizes data exposure while maintaining transparency through detailed overviews.
In this beginner-friendly guide, you’ll learn how to integrate Proton’s services into your daily life for maximum privacy. Discover how pairing Proton Mail with ProtonVPN can shield your IP address and encrypt your communications, or how Proton Drive enables secure file sharing without sacrificing convenience. You’ll also explore practical strategies like allowing two-factor authentication and using email aliases through SimpleLogin to reduce your vulnerability to phishing and spam. By the end, you’ll have a clear understanding of how to use Proton’s ecosystem to reclaim control over your digital privacy.
Proton’s Privacy Ecosystem
TL;DR Key Takeaways :
- Proton offers a comprehensive privacy-first ecosystem, including Proton Mail, ProtonVPN, Proton Drive, Proton Calendar, Proton Pass and SimpleLogin, all designed to protect your digital life with end-to-end encryption and open source software.
- Operating under Switzerland’s strict privacy laws, Proton ensures a higher standard of data protection, with minimal data storage and compliance with legal obligations while safeguarding user content.
- ProtonVPN employs a strict no-logs policy, RAM-only servers and routing through privacy-friendly countries to enhance online anonymity and prevent data storage.
- Unlike ad-driven platforms like Google and Meta, Proton uses a subscription-based model to prioritize user privacy and minimize data collection, making sure greater control over personal information.
- Combining Proton’s tools with privacy-focused practices, such as using encrypted messaging apps, privacy-centric browsers and two-factor authentication, can further enhance digital security and reduce exposure to privacy risks.
Understanding Proton’s Privacy Ecosystem
Proton’s suite of services is carefully designed to secure your data across various platforms, making sure a seamless and private digital experience. Each service plays a unique role in this ecosystem:
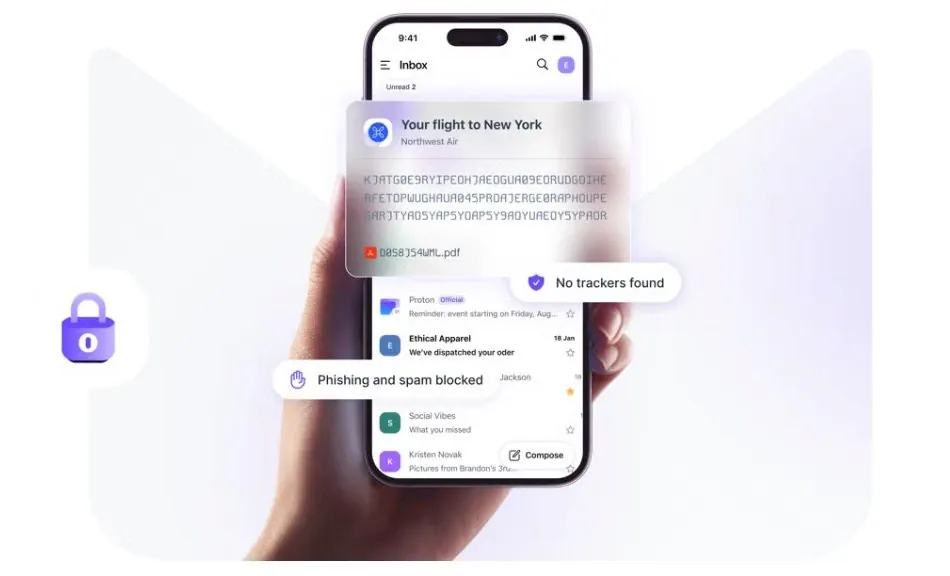
- Proton Mail: A secure email service that uses end-to-end encryption, making sure only you and your recipient can access your messages. This eliminates the risk of third-party interception.
- ProtonVPN: A no-logs virtual private network (VPN) that enhances online anonymity, bypasses censorship and protects your browsing activity from prying eyes.
- Proton Drive: A secure cloud storage solution that encrypts your files, allowing safe sharing and storage without compromising your privacy.
- Proton Calendar: A privacy-focused calendar that allows you to manage events without exposing sensitive data to third parties.
- Proton Pass: An encrypted password manager that safeguards your credentials, making sure they remain protected from unauthorized access.
- SimpleLogin: A tool for creating email aliases, allowing you to shield your primary email address and reduce spam or phishing risks.
Together, these tools form a cohesive, encrypted ecosystem that minimizes your data exposure. Operating under Switzerland’s privacy laws, Proton provides a higher standard of data protection compared to companies based in jurisdictions with weaker privacy regulations. This makes Proton an ideal choice for individuals seeking to reclaim control over their personal information.
Legal Compliance and Metadata Logging
Proton’s commitment to privacy is unwavering, but it must comply with Swiss legal requirements. Under targeted court orders, Proton may be compelled to log limited metadata, such as IP addresses and timestamps, for specific accounts. However, Proton’s encryption ensures that the content of your emails, files and other data remains inaccessible, even to Proton itself. This means that while metadata may be logged in rare cases, the actual content of your communications remains secure.
Proton’s transparency overviews provide detailed insights into the limited number of cases where metadata has been shared. These overviews highlight the stark contrast between Proton and data-heavy platforms like Google and Meta, which routinely collect and store vast amounts of user data. By choosing Proton, you benefit from a service that prioritizes your privacy while maintaining compliance with legal obligations.
Learn more about privacy with other articles and guides we have written below.
- How iOS 26.3 Improves iPhone Privacy and Battery Life
- Samsung Galaxy S26 Ultra Privacy Display Hands On
- How the Galaxy S26 Ultra Redefines Smartphone Privacy
- How to Enable a Privacy Display on iPhone
- Samsung Galaxy S26 Ultra: Privacy Display Explained
- Samsung Galaxy S26 Ultra Privacy Display Explained
- Galaxy S26 Ultra vs. Z Fold 7: A Detailed Comparison
- Samsung Galaxy S27 Ultra: New Privacy Display Coming
- How the Galaxy S26 Ultra Redefines Smartphone Privacy
- Samsung Galaxy S26 Ultra: Privacy, Display, and AI Features
ProtonVPN: A No-Logs Approach to Online Privacy
ProtonVPN is a cornerstone of Proton’s privacy ecosystem, offering a strict no-logs policy that ensures your online activity remains private. Its RAM-only servers are designed to prevent any data from being stored permanently, further enhancing your anonymity. Additionally, ProtonVPN routes your internet traffic through privacy-friendly countries, adding another layer of protection against surveillance.
Regular independent audits verify ProtonVPN’s adherence to its no-logs policy, reinforcing its reputation as a trustworthy option for safeguarding your browsing activity. Whether you’re accessing sensitive information, bypassing censorship, or simply browsing the web, ProtonVPN provides a reliable solution for maintaining your online privacy.
How Proton Differs from Major Tech Platforms
Proton’s approach to privacy sets it apart from major tech platforms like Google and Meta, which rely on ad-driven business models and extensive data collection. By contrast, Proton employs a subscription-based model that minimizes the amount of user data it stores. This significantly reduces the information that could be shared under legal orders, offering a level of privacy that is increasingly rare in today’s digital landscape.
For privacy-conscious users, this distinction underscores Proton’s commitment to protecting your digital footprint. By choosing Proton, you align yourself with a service that prioritizes your privacy over profit, making sure your data remains under your control.
Best Practices for Maximizing Privacy
While Proton’s tools provide a strong foundation for digital security, combining them with additional privacy-focused practices can further enhance your protection. Consider the following recommendations:
- Pair Proton Mail with ProtonVPN: This combination hides your IP address and encrypts your communications, making sure both privacy and security.
- Use encrypted messaging apps: Opt for apps like Signal, which offer end-to-end encryption for secure communication.
- Browse anonymously: Use the Tor network to enhance your online anonymity and avoid tracking.
- Enable two-factor authentication: Add an extra layer of security to your accounts by requiring a second verification step.
- Choose privacy-focused browsers: Use browsers like Brave or Firefox, which include tracker-blocking features to protect your online activity.
- Limit data sharing: Avoid providing unnecessary personal information online and be cautious about the platforms you use.
By layering these tools and practices, you can significantly reduce your exposure to data breaches, surveillance and other privacy risks. Proton’s ecosystem serves as a powerful ally in your quest for digital security, but your habits and choices also play a crucial role in maintaining your privacy.
The Core Principle: Data Minimization
At the heart of Proton’s philosophy is the principle of data minimization—the idea that the safest data is data that is never stored. By adopting secure habits and using privacy-enhancing tools, you can take control of your digital privacy. Whether you’re sending emails, browsing the web, or managing passwords, Proton’s ecosystem offers a comprehensive solution for protecting your data in an increasingly surveillance-driven world.
As the digital landscape continues to evolve, the importance of privacy cannot be overstated. Proton’s services empower you to navigate this landscape with confidence, making sure your personal information remains secure and under your control.
Media Credit: CyberInsider
Disclosure: Some of our articles include affiliate links. If you buy something through one of these links, Geeky Gadgets may earn an affiliate commission. Learn about our Disclosure Policy.